In the era of digitalization, enterprises are generating and storing vast amounts of data to stay competitive in their respective markets. NAS (Network-Attached Storage) systems have proven to be the ideal storage solution for organizations for their data storage requirements, providing high-performance, scalability, and reliable data protection. However, with the rise in ransomware attacks and cyber threats in recent times, organizations must ensure that their NAS systems are equipped with robust data protection, high availability, and backup strategies to safeguard their sensitive data from any unauthorized access or data loss. This blog will discuss how enterprise NAS deployments can ensure data protection and high availability.
Employing Data Backup Strategies
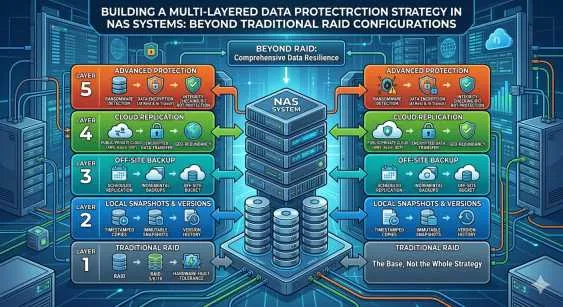
Data backup is the primary method used to ensure data protection and business continuity in enterprise NAS deployments. Organizations can implement either local or remote backup strategies to protect their critical data from loss or corruption. Local backup strategies include snapshotting, where data is copied and saved instantaneously in its current state, and cloning, which involves duplicating an entire volume or file system. Remote backup strategies are offsite backups that protect data and applications from natural disasters, hardware failures, and cyber-attacks. Remote backups can be performed on secondary NAS systems or on cloud storage solutions.
Protecting Data with Encryption
Cyber-attacks are a significant threat to any organization, primarily if they deal with sensitive, confidential data. Enterprises need to protect their data efficiently by encrypting it before storing it on the NAS systems. Data encryption secures data from unauthorized access even if the cyber attacker penetrates the NAS systems. The encrypted data can only be decrypted with an encryption key, ensuring data confidentiality and integrity.
Ensuring High Availability with Redundancy
High availability is crucial in enterprise NAS deployments. Users expect access to their data 24/7, and any downtime can have severe implications on an organization's operations. Redundancy can ensure high availability, where multiple disks, servers, or network connections are deployed to keep critical operations running without interruption. RAID (redundant array of independent disks) is a common redundancy technique used in NAS deployments, providing fault tolerance, increased performance, and data availability.
Regular Security Audits and Patch Management
As cyber threats continuously evolve, it's essential that NAS deployments are subjected to frequent security audits and patch management. Security audits help identify vulnerabilities and weaknesses within the network, while patch management ensures the latest security updates and patches are installed to fix known vulnerabilities. Security audits and patch management must be performed regularly to ensure the NAS systems' security framework remains robust at all times.
Implementing a Disaster Recovery Plan
No matter how robust the NAS systems security framework is, it's essential to implement a Disaster Recovery Plan (DRP) to ensure business continuity in the event of a disaster or an unexpected event. A DRP ensures that the enterprise's critical operations, data, and systems can be quickly restored and resumed in the least amount of time possible. The DRP should be reviewed regularly and tested to ensure that it's operational and delivers the desired outcomes when needed.
Conclusion
NAS systems are the backbone of an enterprise's data storage, providing high-performance and scalability required to meet data storage needs. However, with cyber attacks on the rise, data protection and high availability have become a critical aspect of enterprise NAS deployments. Employing data backup strategies, protecting data with encryption, ensuring high availability with redundancy, regular security audits and patch management, and implementing a disaster recovery plan are all essential aspects of ensuring data protection and high availability in enterprise NAS deployments. Enterprises that can deploy these strategies and frameworks can protect their crucial operations and mitigate the risk of data loss and corruption.




















Sign in to leave a comment.