



Discover how EDR security differs from traditional antivirus, offering advanced threat detection, response, and stronger cyber defense.

Learn how DPDP Rules improve data privacy in India by enhancing user consent, accountability, and secure handling of personal data nationwide.

Learn Data Privacy Compliance best practices to protect customer data, meet regulations, and avoid costly legal penalties effectively.

Learn how cybersecurity for Manufacturing companies protects connected factories, secures OT systems, and prevents cyber threats effectively.

Discover how cloud based endpoint security protects hybrid workforces with real-time monitoring, remote access control, and scalable threat defense.
DPDP business guide India with practical steps for 2026 compliance. Learn data rules, consent, audits, and risk controls for your organization.

Learn how Personal Data Protection laws in India help prevent data leakage with key compliance steps, security practices, and risk mitigation strategies.
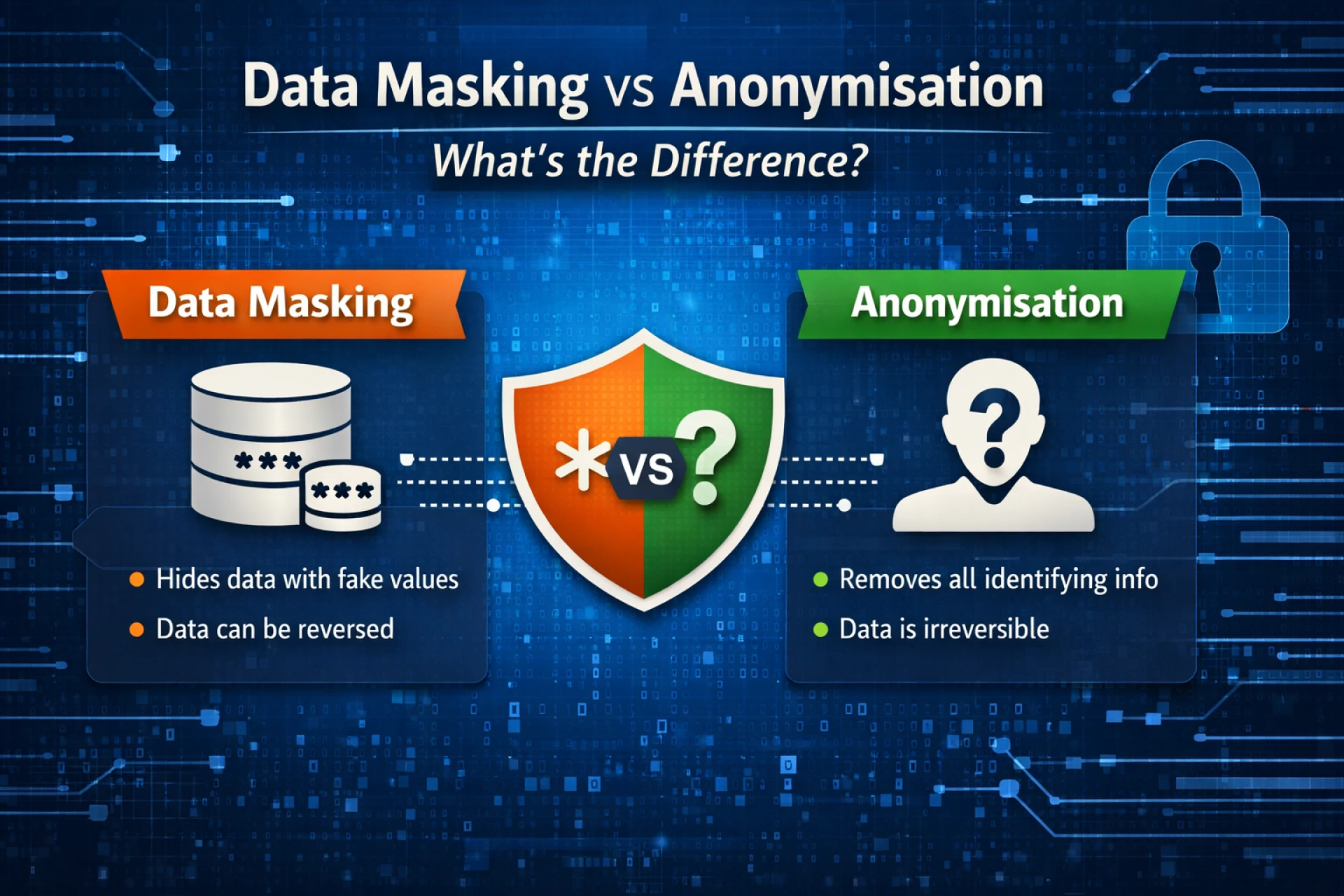
Data masking and anonymisation are essential techniques for protecting sensitive information in modern organisations. While data masking secures data for operational use, anonymisation removes identifying details for long-term privacy. Understanding their differences helps businesses strengthen data security and meet regulatory compliance requirements.
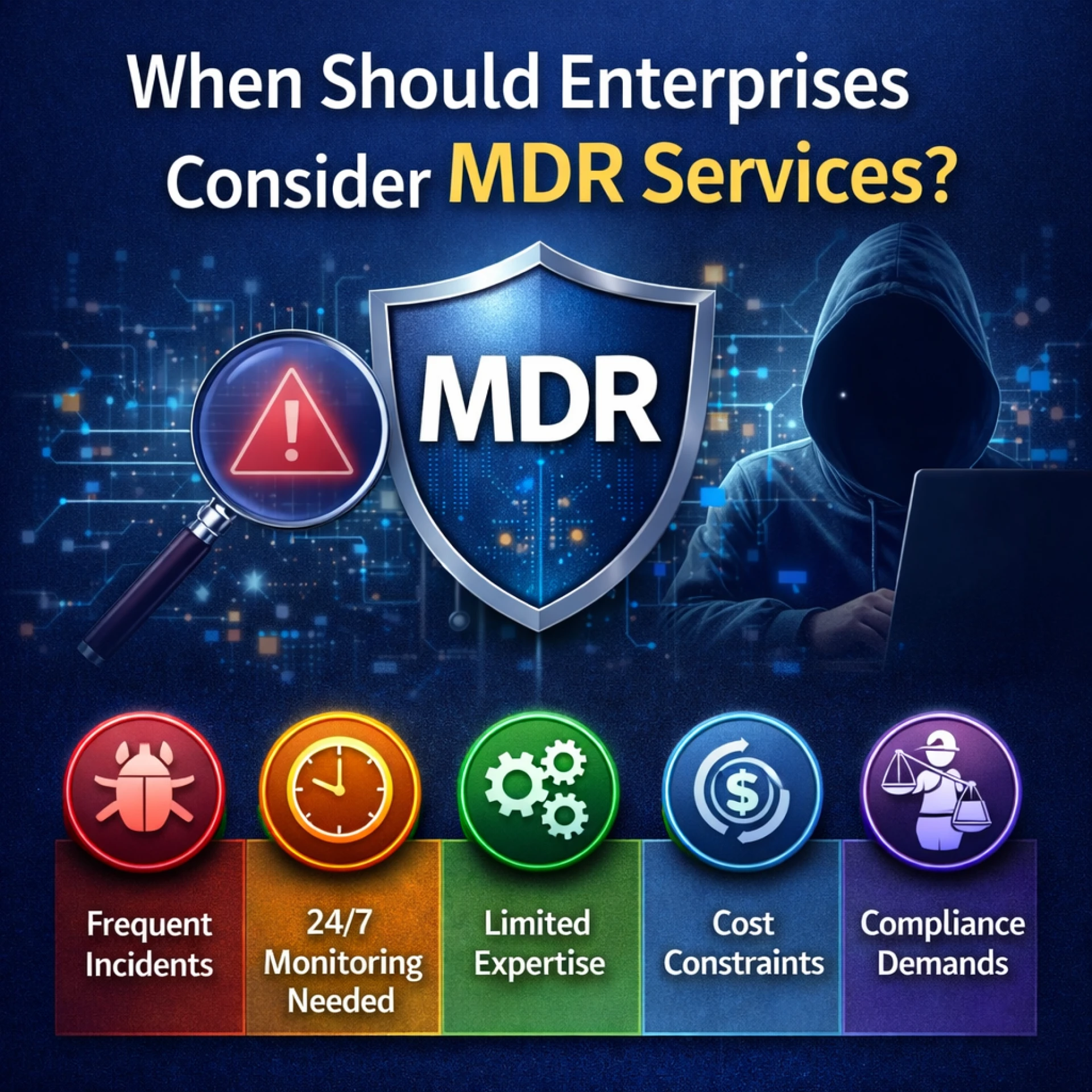
Enterprises facing growing cyber threats, security skill shortages, and limited 24/7 monitoring should consider MDR services. Managed Detection and Response delivers continuous threat monitoring, expert-led investigations, and rapid incident response to reduce breach risks and strengthen overall cyber resilience.
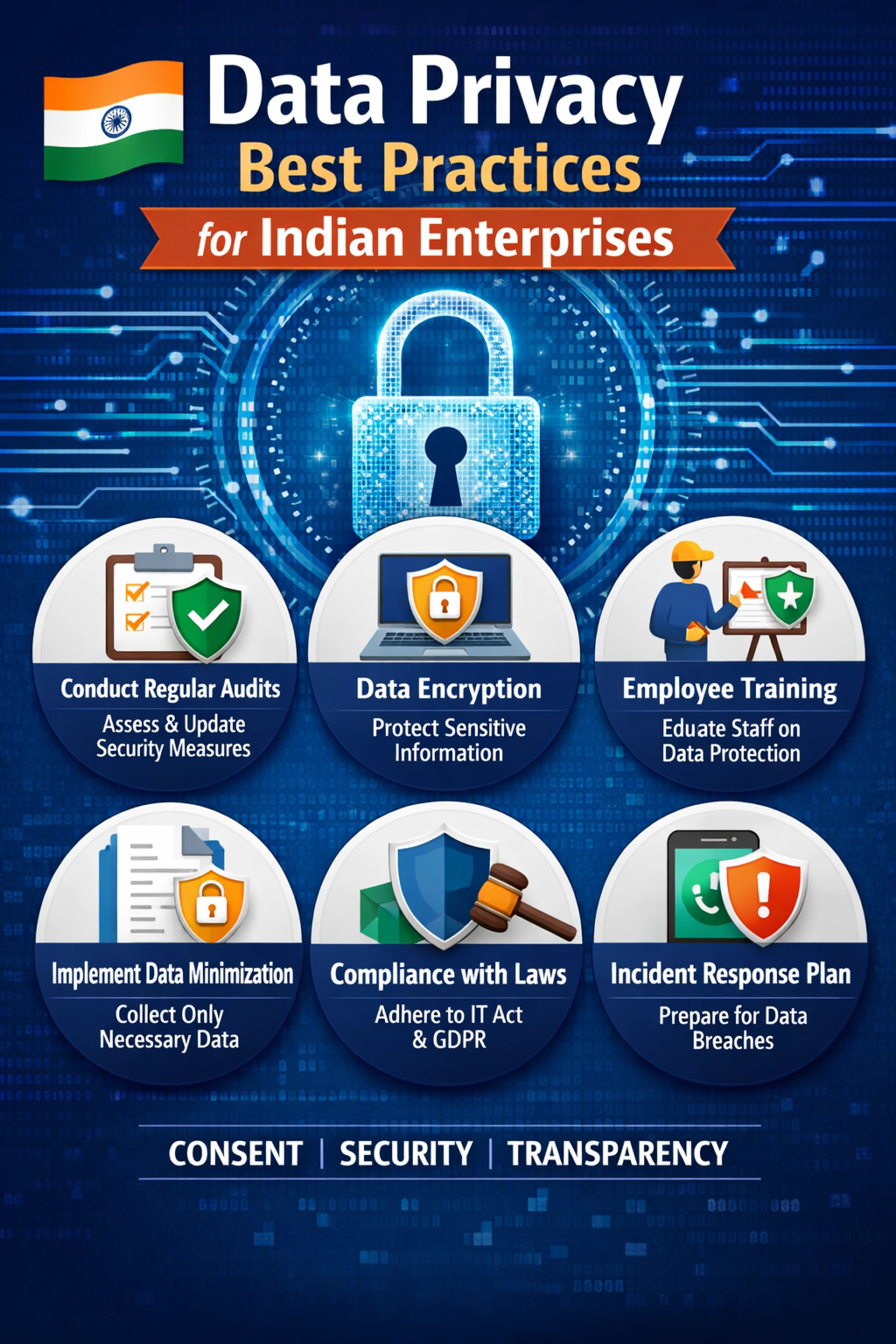
Data privacy best practices are essential for Indian enterprises facing evolving cyber threats and regulatory pressure. A proactive, security-first approach ensures continuous compliance, protects sensitive data, and builds long-term resilience.
Modern enterprises must adopt EDR software to detect advanced threats in real time, gain full endpoint visibility, automate rapid response actions, and strengthen cyber resilience against evolving attacks.
The Cyber Threat Report 2025 in India outlines a troubling trend, as organisations continue to experience increasing volumes of cyberattacks. As India

Enterprises in India are navigating one of the world's most complex threat landscapes. Today, attackers are utilizing artificial intelligence-driven

Financial institutions in India face evolving cybersecurity compliance challenges. Stay compliant with RBI, SEBI, and DPDPA guidelines.

Boost remote device security with Endpoint Protection Cloud using real-time threat detection and centralized management.

Discover how Seqrite XDR, powered by Gen AI and SIA, enhances threat detection, response, and investigation with intelligent automation for advanced cybersecurity defense.

The growth of online banking, phone payments, and web-based investments makes cybersecurity for financial services key now more than ever. Data leaks

In a digital-first era where remote work, cloud computing, and cybercrime are accelerating in parallel, traditional security approaches are proving da