The journey toward safer digital access has moved far beyond traditional login practices. Organizations today seek stronger identity assurance without adding unnecessary effort for users. In the middle of this shift, FIDO Passwordless Authentication emerges as a practical standard that reduces reliance on passwords and strengthens account security with modern, phishing-resistant methods. This roadmap outlines how teams can progress from basic MFA toward a mature, fully password-free environment anchored in FIDO protocols.
Understanding the Shift Toward Passwordless Security
Passwords have long been the weakest element in digital identity. Users reuse them, attackers harvest them, and breaches often trace back to compromised credentials. This has led security teams to adopt multi-factor authentication (MFA). While MFA brings additional layers, many variants still rely on passwords as a primary factor. Over time, the industry recognized the need for a pathway where passwords fade away entirely, replaced by methods tied to user presence, cryptographic verification, and device-bound keys.
This shift is not just technical—it reflects growing expectations for secure digital experiences with less effort required from employees, partners, and customers.
Phase 1 — Strengthening Authentication with MFA
Traditional MFA relies on using something the user knows and something the user has. Common methods include:
- OTPs through SMS or email
- Time-based authenticator apps
- Push notifications
- Hardware tokens
While these options raise the barrier for attackers, they still face certain weaknesses, including:
- Susceptibility to phishing
- Dependence on network connectivity
- Inconsistent user experience
- Ongoing reliance on passwords
This phase represents the important initial step for most teams transitioning toward passwordless strategies.

Phase 2 — Moving Toward Passwordless Foundations
After adopting MFA, organizations often begin exploring approaches that minimize direct password use. These efforts lay the groundwork for a full passwordless environment. Key elements of this stage include:
Biometric Verification for Local Access
Biometric authentication—fingerprints, face data, or iris scans—creates a direct link between the user and the device. While biometrics strengthen identity assurance, they often work in combination with passwords during early adoption.
Hardware-Backed Security Keys
Security keys bring cryptographic protection into the authentication process. Early use may still require passwords, but users gain exposure to possession-based access and device-bound validation.
Conditional Access Policies
Organizations begin applying contextual rules such as login location, device health, or network type. These policies reinforce the authentication flow and reduce password exposure in risky environments.
This stage marks the turning point where passwords start losing their central role.
Phase 3 — Implementing FIDO Authentication Standards
The final stage introduces a protocol built specifically to remove password dependence. FIDO standards use public-key cryptography where keys are generated on the device and never shared. This prevents phishing, eliminates credential theft, and builds strong, user-friendly security.
FIDO2 and WebAuthn for Browser and Platform Access
FIDO2 and WebAuthn allow users to authenticate through:
- Security keys
- Device-based biometrics
- On-device PINs
Each method binds the authenticator to a physical device, reducing threats from remote attackers.
Public-Key Cryptography as the Core
The server stores only the public key. The private key stays on the device and cannot be extracted. During login, users prove possession of the private key without disclosing it. This approach removes the attack surface created by password databases.
Phishing Resistance as a Built-In Advantage
Because authentication relies on cryptographic interaction with the legitimate domain, attackers cannot trick users into entering secrets on fake pages. This makes FIDO methods significantly safer than SMS, OTPs, or push notifications.
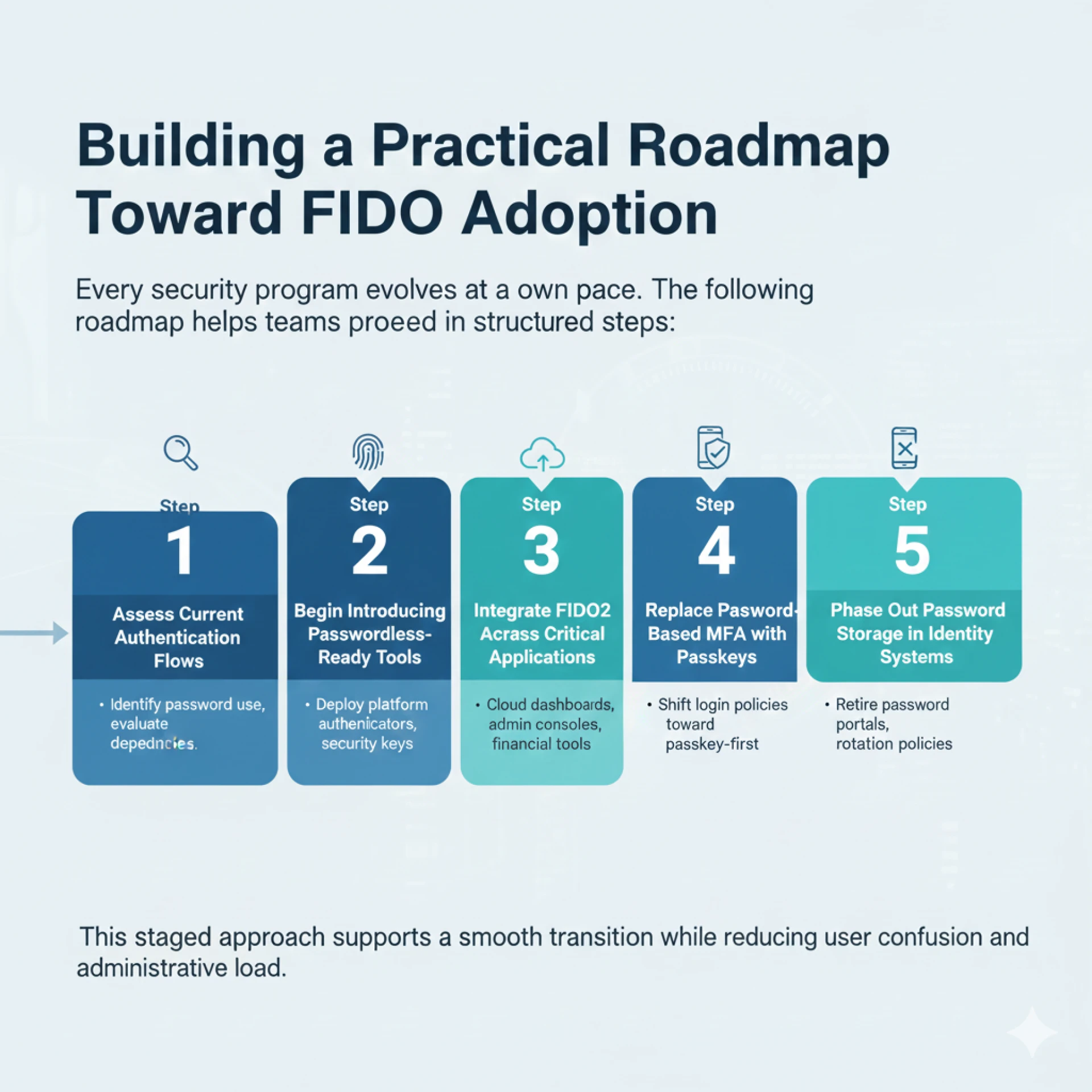
Building a Practical Roadmap Toward FIDO Adoption
Every security program evolves at its own pace. The following roadmap helps teams proceed in structured steps:
Step 1 — Assess Current Authentication Flows
Identify where passwords still appear in user journeys and evaluate which roles or systems depend most heavily on them.
Step 2 — Begin Introducing Passwordless-Ready Tools
Deploy platform authenticators (Windows Hello, Apple Touch ID, Android biometrics) or hardware security keys to familiarize users with local passkey experiences.
Step 3 — Integrate FIDO2 Across Critical Applications
Start with sensitive systems such as cloud dashboards, administrative consoles, or financial tools. Expand based on adoption success.
Step 4 — Replace Password-Based MFA with Passkeys
As users grow comfortable with FIDO authenticators, gradually shift login policies toward passkey-first flows.
Step 5 — Phase Out Password Storage in Identity Systems
Retire password reset portals, password rotation policies, and credential-based recovery workflows.
This staged approach supports a smooth transition while reducing user confusion and administrative load.
Benefits of Reaching Full Passwordless Authentication
Strong Security Without Traditional Credentials
By removing passwords, organizations eliminate phishing, credential stuffing, and brute-force attacks tied to human-created secrets.
Consistent Experience Across Platforms
Users authenticate the same way on mobile apps, browsers, and desktops. No codes. No waiting. No password resets.
Reduced Helpdesk Costs
Password resets consume a large percentage of support tickets. Eliminating them frees IT resources for higher-value tasks.
Compliance Readiness
Many regulations now encourage or require phishing-resistant authentication. FIDO methods meet these expectations naturally through cryptographic validation.
Preparing Teams for a Passwordless Future
Rolling out FIDO authentication is not just a technical shift—user awareness and comfort matter. Clear communication helps set expectations and encourage adoption.
Key elements to highlight include:
- Why fewer passwords improve security
- How passkeys work on personal devices
- What users can expect during enrollment
- How to protect their security keys or local biometric devices
Training supports smoother adoption and reduces friction during onboarding.
A Forward Path Built on Trust, Identity, and Strong Foundations
The passwordless journey is now achievable for organizations of any size. Starting with MFA, progressing through password-reduced workflows, and culminating with FIDO authentication allows teams to build strong identity assurance without increasing complexity. This roadmap provides a structured path where security improves, user experience becomes simpler, and digital systems remain resilient against modern threats.
Conclusion
The shift from MFA to a fully passwordless model reflects a clear priority: stronger protection with fewer hurdles for users. By following a structured roadmap—starting with enhanced MFA, introducing passwordless-ready tools, and adopting FIDO-based authentication—organizations create a security environment grounded in cryptography, user presence, and device trust. This approach removes the risks tied to passwords, simplifies access, and strengthens identity assurance across every application. Moving toward FIDO authentication is not only a technological upgrade but a meaningful step toward a safer, more resilient digital future.















Sign in to leave a comment.