Access Control Systems are essential for securing buildings, data centers, and sensitive areas in any organization. However, even the most robust access system can face challenges when there is a power outage or network downtime. Ensuring that security remains uncompromised during such events is critical to protecting assets, maintaining safety, and minimizing operational disruption. By implementing best practices and leveraging modern technology, organizations can maintain effective access control security systems even under adverse conditions.
Access control systems rely on electricity and network connectivity to function efficiently. Power interruptions, network failures, or hardware malfunctions can temporarily disable doors, turnstiles, and electronic locks, potentially creating security vulnerabilities. Preparing for these scenarios ensures that employees, visitors, and security teams can continue to operate safely while maintaining control over access points.
Challenges During Power or Network Downtime
Understanding the challenges that arise during downtime helps organizations plan effective solutions. Some common issues include:
- Locked or Unlocked Doors
- In the event of a power failure, electronic locks may default to a locked or unlocked state depending on their fail-safe or fail-secure design. Fail-safe locks unlock when power is lost to allow safe evacuation, while fail-secure locks remain locked to maintain security. Organizations must choose the appropriate mechanism for each area.
- Inaccessible Access Logs
- Network downtime can prevent access logs from being transmitted to central servers. This may delay auditing, monitoring, or investigations if events are not recorded in real time.
- Disruption of Authentication Methods
- Many access control systems rely on network connectivity to verify credentials against a central database. During downtime, biometric scanners, card readers, or mobile credentials may fail to authenticate users.
- Impact on Emergency Response
- In emergencies, security personnel may need to override locks or control doors remotely. Network or power failures can impede these actions, potentially delaying evacuation or response.
Strategies for Maintaining Access Control
Organizations can adopt several strategies to ensure accesscontrol systems remain functional during power or network interruptions:
- Uninterruptible Power Supply (UPS) Systems
- Installing UPS systems for critical access points ensures that doors, turnstiles, and electronic locks continue to function during short-term power outages. UPS systems provide backup power to keep access control security systems operational until normal power is restored.
- Battery-Backed Locks and Controllers
- Many modern access control systems include battery backups within controllers and locks. These batteries provide emergency power to maintain functionality, allowing secure access and proper logging even if the main power supply is interrupted.
- Fail-Safe vs Fail-Secure Configurations
- Choose appropriate fail-safe or fail-secure configurations based on the area’s security and safety requirements. Emergency exits or high-traffic zones may use fail-safe locks to allow safe egress, while data centers and sensitive areas may use fail-secure locks to prevent unauthorized entry.
- Local Authentication Capabilities
- Access systems with local credential verification can continue to operate without network connectivity. By storing credential data locally on readers or controllers, doors can authenticate users and maintain logs until network access is restored.
- Redundant Network Infrastructure
- Implementing redundant network connections reduces the risk of downtime. Dual network paths, cellular backup connections, or mesh networks help ensure continuous communication between access points and central servers.
- Manual Override Options
- For critical security points, manual override options such as mechanical keys or emergency release switches provide an additional layer of reliability during power or network failures. These mechanisms allow authorized personnel to operate the access system safely.
Best Practices for Access Control During Downtime
To minimize the impact of downtime on security and operations, organizations should follow these best practices:
- Regular Testing – Periodically test UPS systems, battery backups, and failover networks to ensure they function correctly when needed.
- Segment Critical Areas – Prioritize power and network backup for high-security zones and sensitive areas to maintain operational integrity.
- Maintain Access Logs Locally – Configure access control systems to store logs locally during network outages and synchronize them with central servers once connectivity is restored.
- Develop Emergency Protocols – Create clear procedures for staff to follow during power or network downtime, including emergency access procedures, manual overrides, and communication protocols.
- Monitor Backup Systems – Continuously monitor the health of UPS systems, batteries, and redundant networks to prevent unexpected failures.
- Train Security Personnel – Ensure staff are familiar with emergency procedures, manual override operations, and backup authentication methods.
Leveraging Modern Technology
Modern access control systems offer advanced features that improve resilience during power or network downtime:
- Cloud-Based Access Control with Local Failover
- Cloud-enabled access control systems can continue operating locally even when internet connectivity is lost. Local controllers store credentials and logs, synchronizing with the cloud once connectivity is restored.
- Mobile and Offline Credentials
- Mobile access solutions allow users to authenticate using stored credentials on smartphones or wearables. These offline credentials function even when network access is unavailable.
- Remote Monitoring and Alerts
- Analytics and monitoring tools can notify security personnel of system status, power interruptions, or battery failures in real time. This enables proactive management and rapid response.
- Smart Lock Technology
- Advanced smart locks can switch automatically between fail-safe and fail-secure modes depending on the situation, providing both security and safety during downtime events.
Planning for Resilience
Building resilience into accesscontrol systems involves more than technology. Organizations should incorporate planning, testing, and continuous improvement:
- Risk Assessment – Identify critical access points, potential failure scenarios, and their impact on security and operations.
- Redundancy Planning – Implement redundant power, network, and backup authentication systems for high-priority areas.
- Regular Audits – Review access control policies, configurations, and logs to ensure downtime procedures are effective and up to date.
- Continuous Improvement – Update systems and procedures based on lessons learned from tests, incidents, or technology upgrades.
Conclusion
Power and network downtime can pose significant challenges to access control security systems, but with careful planning and modern technology, organizations can maintain security and operational continuity. Implementing UPS systems, battery backups, local authentication, redundant networks, and clear emergency protocols ensures that access systems remain functional when it matters most.
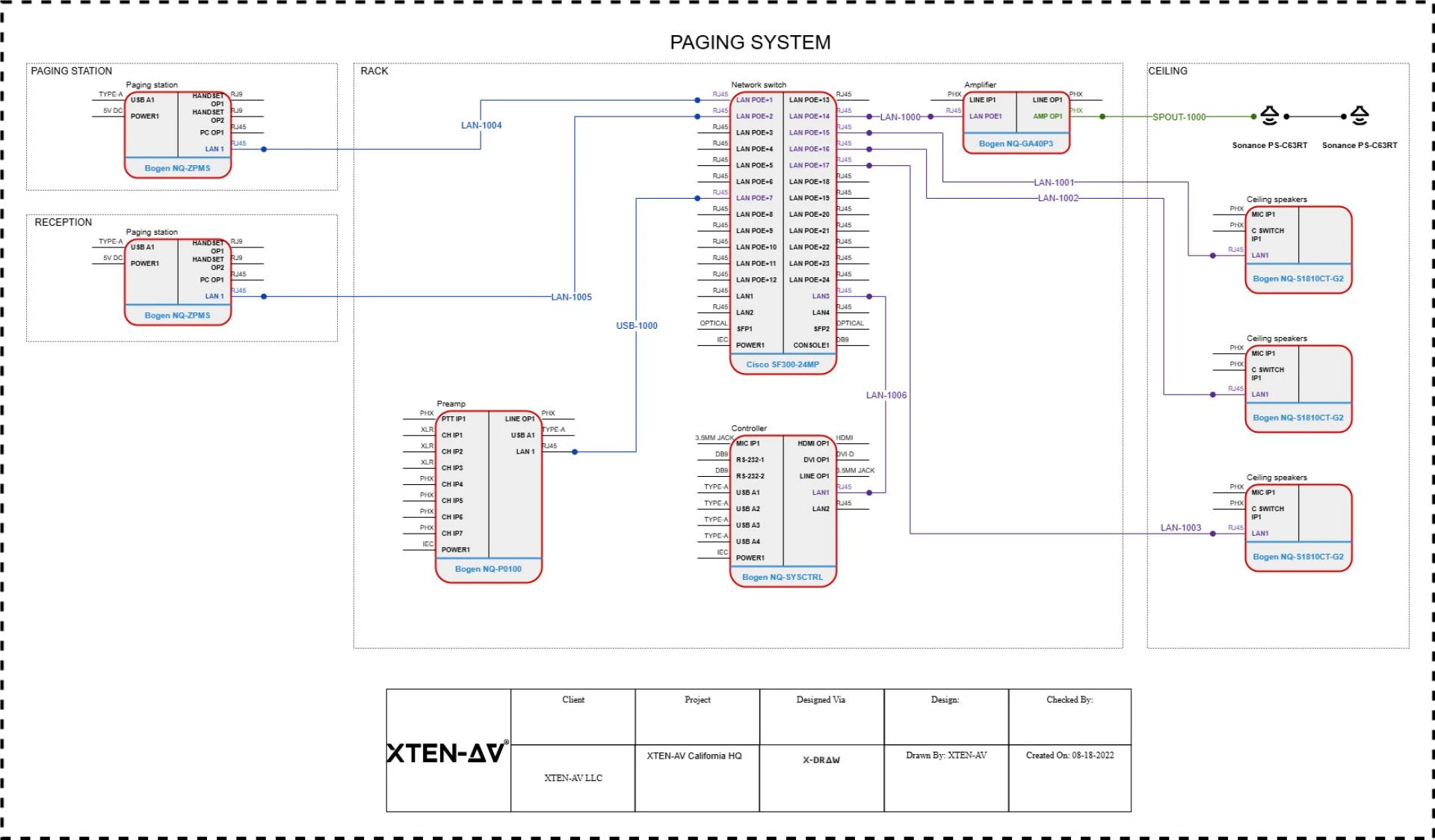
XTEN-AV provides solutions that help organizations manage access control effectively during power or network interruptions. By integrating resilient technology, automated backups, and emergency protocols, businesses can ensure safety, maintain security, and minimize disruptions even during unexpected downtime.
Read more: https://topbizlists.com/how-to-manage-emergency-access-without-compromising-security/


















Sign in to leave a comment.