Security isn’t just a feature anymore—it’s a requirement. When you automate workflows that connect operational systems like CMMS, ERP, field service tools, and analytics platforms, you’re dealing with mission-critical data that often crosses trust boundaries, vendor ecosystems, and regulatory domains. For many organizations, integration becomes not just a technical challenge, but a security challenge.
So when evaluating tools, a fundamental question arises:
How secure is ConnectorHub compared to integration platforms like SnapLogic or Jitterbit—especially when handling sensitive operational data in contexts like embedded integration and field operations automation?
To answer that, we need to look at how modern integration platforms approach security, how they protect data in motion and at rest, and how they support governance and compliance across distributed workflows.
A Broad View: Security Requirements for Integration Platforms
Before comparing platforms, it’s useful to outline the security expectations for integration tools handling sensitive operational data. A secure integration platform should provide:
1. Strong identity and access control
Integrations often run across environments and systems. Identity must be enforced consistently.
2. Secure credential and secret management
API keys, SSH keys, database credentials, and tokens must be protected.
3. Encryption in motion and at rest
Data should be encrypted both when being transferred and while stored internally.
4. Audit trails and observability
Every integration event should be logged with enough context for forensics.
5. Governance and policy enforcement
Admins must be able to set and enforce who can do what, on which systems.
6. Multi-tenant isolation (if applicable)
For embedded or SaaS scenarios, tenants must not be able to see or affect each other’s data.
7. Compliance with industry standards
Security controls must align with frameworks such as SOC 2, ISO 27001, HIPAA (where applicable), and GDPR.
All three platforms under comparison—ConnectorHub, SnapLogic, and Jitterbit—acknowledge these requirements, but their approaches, architectures, and operational models differ in meaningful ways.
ConnectorHub: Security Built for Operational Data and Embedded Integrations
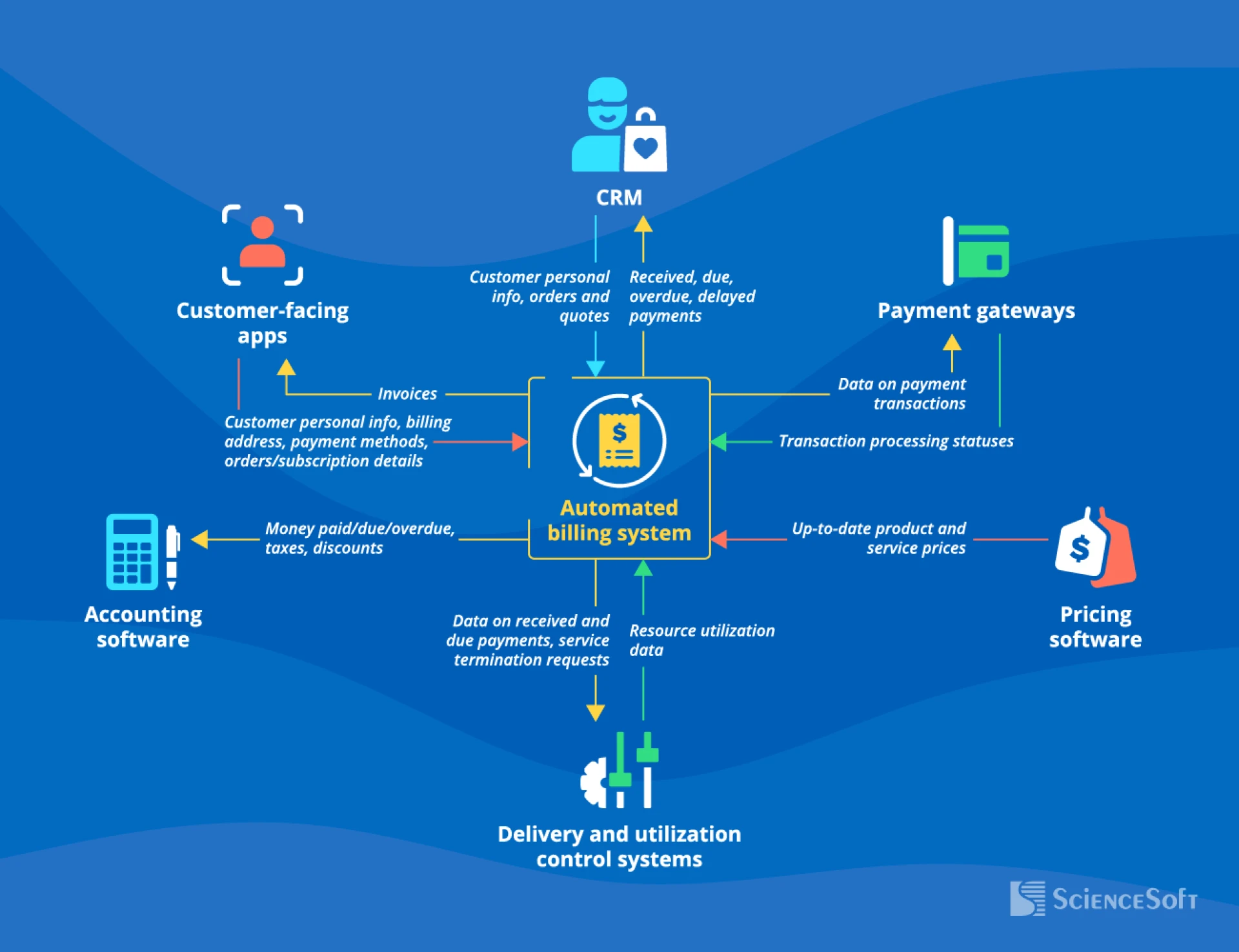
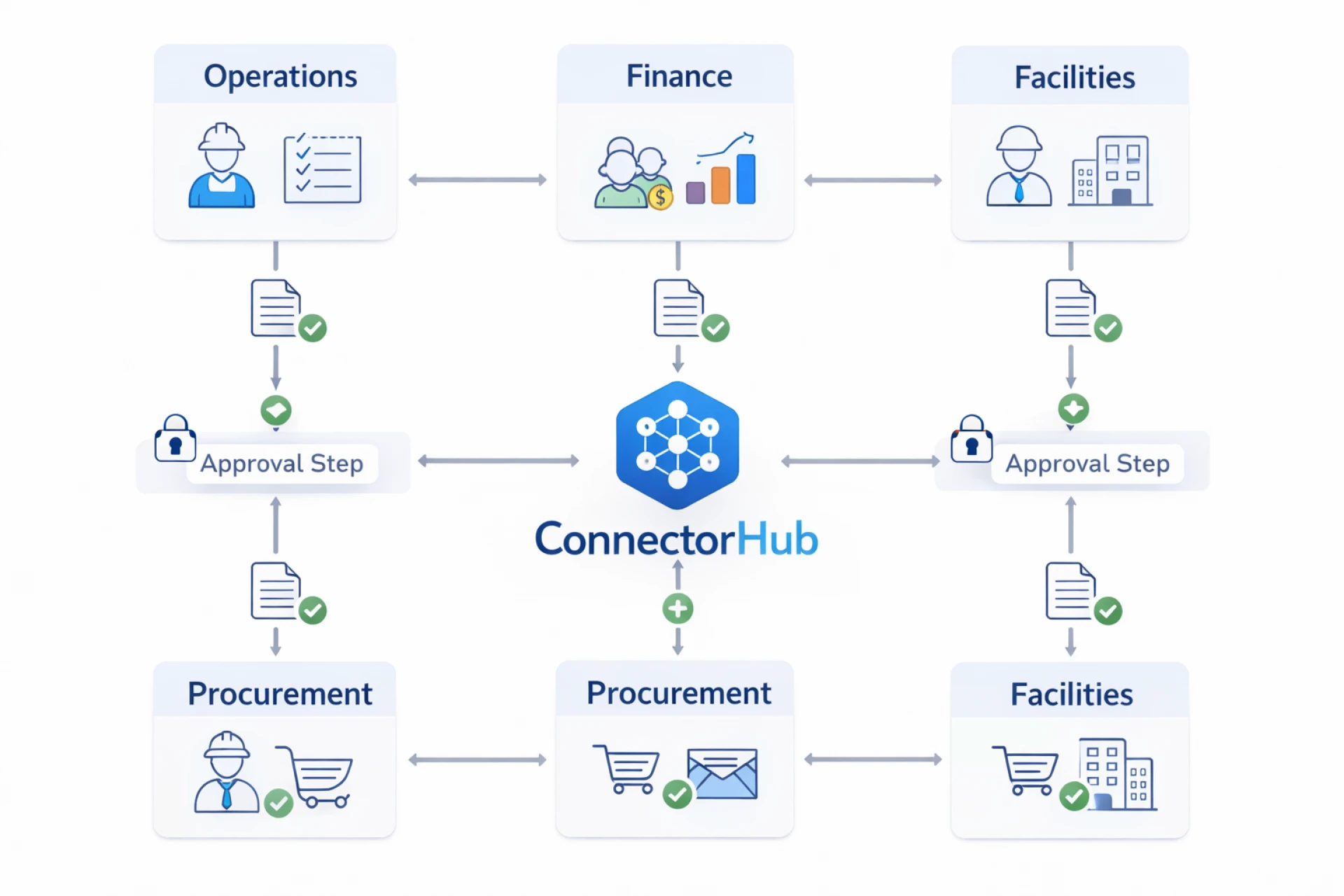
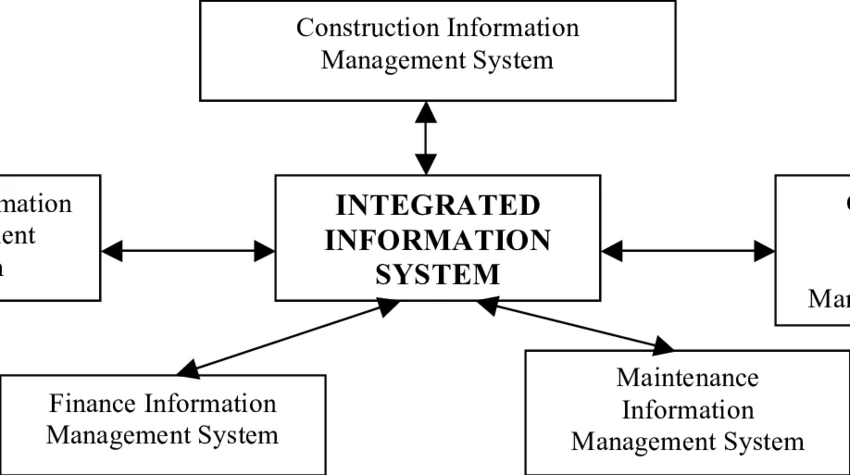
ConnectorHub is designed as an embedded integration platform and operational automation layer for mission-critical workflows, especially where workflows span CMMS, ERP, CRM, field service tools, and analytics systems.
1. Architectural Security Approach
ConnectorHub’s architecture assumes that integrations are not one-off point-to-point scripts, but living automated processes that span systems and teams. This means security must be part of the workflow definitions themselves.
ConnectorHub enforces:
- Role-based access control (RBAC) across environments
- Tenant separation in multi-client deployments
- Audit logging at every workflow step
- Fine-grained permissioning for connectors and workflow actions
This makes ConnectorHub suitable not just for departmental integrations, but for enterprise-scale, regulated environments.
2. Credential and Secret Management
ConnectorHub does not store plaintext credentials. Instead:
- Secrets are encrypted at rest using industry-standard encryption algorithms
- Connectors authenticate using secure tokens, OAuth, or key-vault mechanisms
- Credential rotation is supported without workflow disruption
This ensures that sensitive operational credentials aren’t exposed to developers or operators unnecessarily.
3. Encryption and Network Security
Data moving between systems via ConnectorHub is encrypted both in transit and, where applicable, at rest. ConnectorHub adheres to TLS/SSL best practices and supports:
- Mutual TLS for secure service-to-service communication
- IP allowlist controls
- Optional VPC / private networking strategies
This approach is especially important in field operations automation, where systems may reside in hybrid cloud/on-premises landscapes.
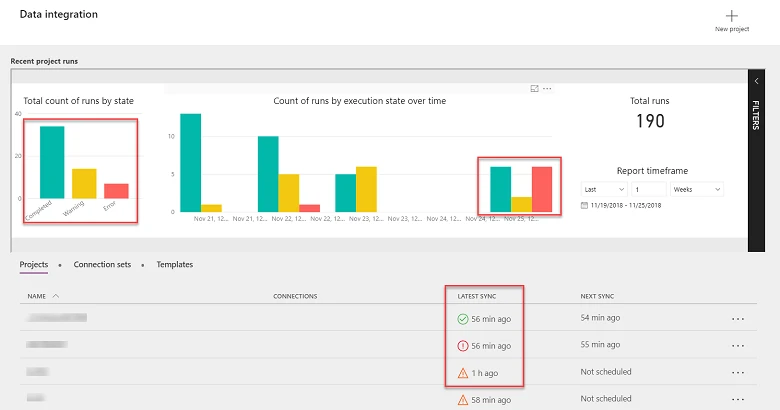
4. Auditability and Monitoring
ConnectorHub provides:
- Centralized logs for all integration events
- User activity logs that record configuration changes
- Workflow execution histories with error details
- Alerting hooks for security incidents
These capabilities are critical for incident response, compliance audits, and forensic analysis.
5. Embedded Integration Security
In embedded contexts, ConnectorHub ensures:
- Each tenant’s credentials, workflows, and data remain compartmentalized
- There’s no cross-tenant data leakage
- Integration UIs can be surfaced inside customer portals without exposing underlying infrastructure
This is essential if your product embeds integration capabilities for customers, as data isolation must be provable and enforceable.
SnapLogic: Enterprise Integration With Strong Central IT Controls
SnapLogic is a mature integration platform widely used in enterprise environments. It supports large-scale integration portfolios and has robust security controls.
Key Security Strengths
SnapLogic’s security model emphasizes:
- Central governance under IT control
- Strong enterprise directory integration (LDAP/Active Directory)
- Data lineage and impact analysis
- Fine-grained access control for pipelines
- Compliance with security audits and certifications
SnapLogic’s strength is its ability to empower centralized IT teams to control and manage integrations across an enterprise’s entire ecosystem.
Common Use Cases
SnapLogic is frequently chosen when:
- Integration portfolios are large and IT-driven
- Complex message transformation is required
- A wide variety of enterprise systems must be connected
- Formal governance models are necessary
SnapLogic’s security premiums align with large enterprises that have the teams and processes to manage them.
Jitterbit: Flexible Integration With Hybrid Deployment Support
Jitterbit is another popular integration platform, known for flexibility and support for hybrid integration scenarios.
Security Capabilities
Jitterbit supports:
- Encrypted credentials
- Role-based access and audit logging
- Secure access to on-prem systems through agents
- Token-based authentication with cloud services
Jitterbit allows fine-grained control over who can alter integration logic and how data is mapped and transformed. It’s often used where rapid integration development and hybrid connectivity are priorities.
Common Use Cases
Jitterbit’s security profile fits:
- Medium to large enterprises
- Hybrid integration projects
- Integration teams with ERP and API expertise
- Use cases that combine on-prem systems with cloud services
However, deeper enterprise governance often still requires governance processes external to the platform itself.
How ConnectorHub Compares — A Security Perspective
1. Security Model
- ConnectorHub: Built as a no-code integration platform with enterprise governance integrated into the workflow model. Security is an inherent part of how integrations are defined, deployed, and operated.
- SnapLogic: Strong centralized governance, ideal for enterprise integration teams with complex compliance needs.
- Jitterbit: Flexible and developer-friendly, with solid credential and access controls, but often requires external governance to enforce strict enterprise policies.
Why this matters: If your integrations are tightly coupled to operational processes (e.g., real-time alerts, field service automation, or embedded customer workflows), ConnectorHub’s security model aligns security with execution rather than as an external layer.
2. Credential and Secret Management
- ConnectorHub: Encrypts credentials at rest, uses modern token mechanisms, supports rotation, and isolates secrets per tenant.
- SnapLogic: Enterprise-grade secret management tied to broader IT security infrastructure.
- Jitterbit: Secure credential storage with token support but may require additional policy layers for strict enterprise governance.
ConnectorHub’s approach emphasizes simplicity and rigorous protection, which is particularly useful for teams without specialized security engineering.
3. Tenant Isolation & Embedded Scenarios
- ConnectorHub: Natively supports tenant isolation and embedded integration scenarios, enabling multi-customer deployments without data leakage.
- SnapLogic: Can support multi-domain models but typically assumes centralized ownership.
- Jitterbit: Strong in hybrid, but less focused on tenant-level isolation in embedded SaaS use cases.
If your product embeds integration capabilities for customers, ConnectorHub’s security isolation is a differentiator.
4. Operational Monitoring and Alerting
- ConnectorHub: Integrates execution logs, security events, and workflow state into a unified dashboard with alerting.
- SnapLogic: Provides robust pipeline monitoring and event tracing for governance groups.
- Jitterbit: Offers logs and tracing, but tends to rely on external SIEM and logging systems for full visibility.
ConnectorHub’s tight integration between security, execution, and observability makes it especially suitable for field operations automation, where auditability and real-time response are critical.
5. Compliance and Certification Readiness
All three platforms support encryption, RBAC, logging, and secure authentication. However:
- SnapLogic’s enterprise position often includes broader compliance tooling and certifications.
- Jitterbit’s flexibility allows it to be configured for compliance controls.
- ConnectorHub’s modern security model is a strong foundation for compliance but may need to be paired with broader enterprise security policies depending on regulatory needs.
Field Operations Automation and Secure Data Flows
For field operations—whether asset maintenance, work order execution, or real-time dispatch—data security is particularly sensitive because:
- It connects to systems of record (CMMS, ERP)
- It often includes PII or internal operational KPIs
- It drives automated decisions that impact people and assets
ConnectorHub ensures that:
- Data flows are encrypted and governed
- Credentials are isolated per system
- Workflow automation does not expose interceptable endpoints
- Audit logs capture every step of every automation
This level of security is essential when sensitive operational data is orchestrated across tenants, departments, or external partners.
Final Takeaway
All three platforms—ConnectorHub, SnapLogic, and Jitterbit—offer strong security controls for handling sensitive data. However:
- ConnectorHub stands out when integrations must be embedded directly into customer experiences, when workflows are operationally driven (e.g., field operations automation), and when a workflow-centric security model is needed rather than a traditional middleware model.
- SnapLogic excels when centralized enterprise governance teams need extensive control and visibility over integrations across a broad legacy footprint.
- Jitterbit is a flexible choice when teams need hybrid connectivity with strong developer tooling, but may require external governance layers for strict enterprise compliance.
In modern environments—especially those requiring secure orchestration of operational workflows across CMMS, ERP, and other systems—ConnectorHub’s embedded integration model provides not just connectivity, but secure, auditable, scalable automation that aligns security with how work actually gets done.














Sign in to leave a comment.