Network Attached Storage (NAS) systems have become the backbone of modern data management for businesses of all sizes. Whether you're managing terabytes of customer data or scaling your infrastructure to meet growing demands, implementing proper NAS best practices ensures your storage solution delivers optimal performance while keeping your critical information secure.
This comprehensive guide covers essential strategies for maximizing your NAS performance and implementing robust protection measures. You'll discover practical techniques for configuration, security protocols, and scaling strategies that will help you build a reliable, efficient storage infrastructure.
Understanding Your Network Attached Storage Foundation
Before diving into optimization techniques, it's crucial to understand what makes NAS systems unique. Unlike traditional direct-attached storage, network attached storage operates over your network, providing centralized file storage accessible by multiple users and devices simultaneously.
The key advantage lies in its flexibility and scalability. Scale out NAS storage solutions allow organizations to expand capacity by adding additional nodes to the existing cluster, creating a distributed storage environment that grows with your needs.
Modern NAS systems offer several deployment options, from single-unit devices perfect for small businesses to enterprise-grade scale out NAS storage architectures that can handle petabytes of data across multiple locations.
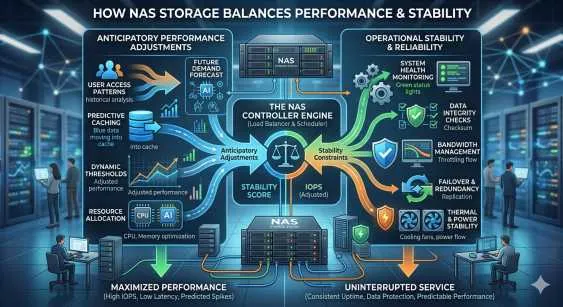
Performance Optimization Strategies
Network Infrastructure Considerations
Your network backbone determines NAS performance more than any other single factor. Gigabit Ethernet should be considered the minimum standard, with 10 Gigabit Ethernet recommended for high-performance environments.
Network segmentation plays a vital role in maintaining consistent performance. Dedicating separate VLANs for storage traffic prevents bandwidth competition with general network usage, ensuring your NAS operations maintain priority access to network resources.
Consider implementing link aggregation (LACP) to combine multiple network interfaces, effectively multiplying your available bandwidth while providing redundancy in case of interface failure.
Storage Configuration Best Practices
RAID configuration directly impacts both performance and data protection. RAID 10 offers excellent performance with redundancy, making it ideal for high-transaction environments. RAID 6 provides superior protection against multiple drive failures while maintaining reasonable performance for less demanding applications.
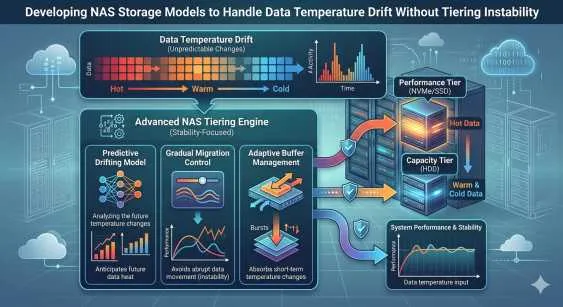
SSD caching can dramatically improve performance for frequently accessed files. Many modern NAS systems support tiered storage, automatically moving hot data to faster storage media while keeping cold data on cost-effective traditional drives.
Regular defragmentation of traditional hard drives maintains optimal read/write speeds, though this process should be scheduled during low-usage periods to minimize performance impact on active users.
File System and Protocol Optimization
Choosing the appropriate file sharing protocol affects both performance and compatibility. SMB/CIFS works well in Windows-dominated environments, while NFS typically offers better performance in mixed or Linux-heavy networks.
Enable jumbo frames (9000 MTU) on both your NAS and network infrastructure to reduce packet overhead, particularly beneficial for large file transfers common in video production or backup operations.
Consider implementing file system quotas to prevent any single user or application from consuming excessive storage space, which can lead to performance degradation across the entire system.
Essential NAS Security Measures
Access Control and Authentication
Implementing robust NAS security starts with proper user authentication. Multi-factor authentication adds a critical security layer, preventing unauthorized access even if passwords are compromised.
Role-based access control (RBAC) ensures users can only access data relevant to their responsibilities. Create specific groups for different departments or project teams, assigning permissions at the group level rather than managing individual user access.
Regular access audits help identify and remove unnecessary permissions. Quarterly reviews of user access rights ensure former employees or contractors no longer have system access, and current users maintain appropriate permission levels.
Network Security Protocols
Enable encryption for all data transmission between clients and your NAS system. SMB 3.0 and later versions include built-in encryption capabilities that protect data in transit without significant performance penalties.
Firewall configuration should restrict NAS access to authorized network segments only. Implement IP whitelisting for administrative access, limiting management interface access to specific trusted IP addresses.
VPN access provides secure remote connectivity for authorized users working from outside your network perimeter, eliminating the need to expose NAS security services directly to the internet.
Data Protection and Backup Strategies
The 3-2-1 backup rule remains the gold standard: maintain three copies of critical data, store them on two different media types, and keep one copy offsite. Your NAS can serve as one component of this strategy, but never as the sole backup solution.
Implement automated backup schedules for different data types based on their criticality and change frequency. Customer databases might require hourly backups, while archived documents could be backed up daily or weekly.
Consider implementing versioning for critical files, allowing recovery of previous versions if files become corrupted or inadvertently modified. Many NAS systems support snapshot technologies that create point-in-time copies with minimal storage overhead.
Monitoring and Maintenance Protocols
Performance Monitoring
Establish baseline performance metrics during normal operations, including throughput rates, response times, and resource utilization. This baseline helps identify performance degradation before it impacts users.
Set up automated alerts for critical thresholds such as disk space utilization, temperature warnings, and hardware failures. Proactive monitoring prevents small issues from becoming major outages.
Regular performance reviews help identify trends and capacity planning needs. Monthly reports showing storage growth rates, user activity patterns, and system performance metrics guide future infrastructure decisions.
Preventive Maintenance
Schedule regular firmware updates during maintenance windows to ensure your NAS system includes the latest security patches and performance improvements. Test updates in non-production environments when possible.
Implement regular disk health monitoring using SMART data to identify drives showing early warning signs of failure. Proactive drive replacement prevents unexpected outages and potential data loss.
Clean physical components regularly, particularly fans and air filters in rack-mounted units. Proper ventilation maintains optimal operating temperatures and extends hardware lifespan.
Planning for Growth and Scalability
Scale out NAS storage architectures provide the flexibility to expand capacity and performance as your organization grows. Plan your initial deployment with future expansion in mind, ensuring adequate network infrastructure and rack space for additional nodes.
Consider your data growth patterns when planning capacity. Organizations typically experience 20-40% annual data growth, though this varies significantly by industry and business model.
Evaluate your disaster recovery requirements as you scale. Larger storage deployments may benefit from geographically distributed nodes or cloud integration for offsite data protection.
Building Your Resilient Storage Infrastructure
Implementing these Network Attached Storage best practices creates a foundation for reliable, secure, and scalable data storage. Success requires ongoing attention to performance monitoring, security updates, and capacity planning.
Start with a thorough assessment of your current storage needs and growth projections. Focus on implementing robust NAS security measures from day one, as retrofitting security controls is more complex and disruptive than building them into your initial deployment.
Remember that storage infrastructure is an investment in your organization's future. Proper planning, implementation, and maintenance of your NAS environment will provide years of reliable service while protecting your most valuable digital assets.



















Sign in to leave a comment.