Ransomware tactics have shifted. In the past, attackers simply encrypted live production data and demanded a payout. Today, sophisticated threat actors play a longer game. They silently infiltrate a network, conduct reconnaissance, and compromise administrative credentials. Once they have elevated privileges—often referred to as "root" or "admin" access—they hunt down your backups.
If an attacker controls the administrator account for your storage, they typically have the power to delete volumes, format drives, or change retention policies. This is the "inside job" scenario, even if the "insider" is actually a hacker sitting halfway across the world.
To combat this, modern enterprise storage has evolved. The latest generation of the NAS system offers a feature called immutable storage, designed to withstand even the most powerful user on the network. But how can software tell a system administrator "no"?
Here is how advanced storage solutions enforce data permanence against compromised admin credentials.
The Problem with Standard Permissions
In a traditional IT environment, the ‘root’ or ‘super-admin’ user is god-like, and this same level of control often extends to a NAS system. They can create files, modify system clocks, change passwords, and wipe hard drives. Standard file permissions (Read/Write/Execute) apply to standard users, but the root user bypasses these checks across the NAS system and underlying infrastructure.
When a ransomware gang steals these credentials, they use legitimate administrative tools to destroy data. They might log into the ISCSI NAS management console and simply select "Delete Volume." Because the system recognizes the user as an authorized administrator, it executes the command without hesitation.
Immutability changes this architecture by removing the "delete" and "modify" capability from every user, including the root account, for a set period.
WORM and Object Locking
The core technology behind immutability is WORM (Write Once, Read Many). Once a file is written to the disk and locked, it cannot be changed or deleted until a specific retention period expires.
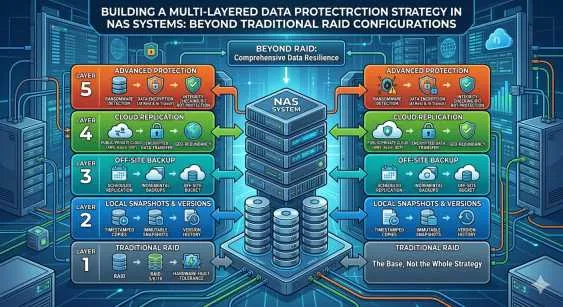
Modern NAS storage solutions often implement this using Object Locking, a feature popularized by cloud storage but now common in on-premise hardware. When configuring immutability, there are generally two modes:
- Governance Mode: This prevents standard users from deleting files, but allows a specific group of administrators to bypass the lock. This is useful for compliance but useless against ransomware with admin credentials.
- Compliance Mode: This is the nuclear option. In Compliance Mode, no one can delete the data. Not the CEO, not the IT Director, and not the hacker who stole their passwords. The data is locked until the retention timer runs out.
Defending Against "Clock Attacks"
If an attacker cannot delete the file because the retention timer hasn't expired, their next logical move is to speed up time. If a file is locked for 30 days, the hacker might try to change the NAS system clock to make the system think 31 days have passed, effectively expiring the lock.
To prevent this, high-security NAS systems utilize a secure, tamper-proof clock.
NTP Fingerprinting
The system relies on Network Time Protocol (NTP) to sync time, but it applies strict variances. If an admin tries to jump the clock forward by months or years instantly, the system rejects the change.
Hardware-Based Clocks
Some enterprise-grade hardware includes an independent internal clock that runs separately from the operating system's system time. Even if an attacker gains root access to the OS and changes the date via the command line, the immutable locking mechanism references the hardware clock, which remains accurate.
The Role of API Barriers
One of the most effective ways NAS storage solutions prevent admin-level attacks is by severing the link between the management interface and the underlying storage kernel.
In a standard setup, if you log into the web interface, you can format the drives. In an immutable setup, the "Delete" command is removed from the API entirely for locked objects. Even if a hacker scripts a command to delete the data, the storage operating system returns an error. The code required to execute the deletion simply does not exist for that specific data set while the lock is active.
This is particularly relevant for iSCSI NAS deployments. While iSCSI creates block-level storage that looks like a local hard drive to the server, the snapshotting happens at the NAS level. Even if the server (and the attacker) thinks they have formatted the iSCSI drive, the NAS retains immutable snapshots in the background that cannot be touched by the iSCSI initiator.
Air-Gapping Within the Box
Physical air-gapping involves disconnecting a backup drive from the network entirely. While secure, it is manual and slow. Modern NAS systems create a "logical air gap."
The system isolates the management plane (where admins log in) from the data plane (where data lives). To make critical changes to the immutability policy—such as attempting to turn it off—some systems require a physical token, a smart card, or a challenge-response code that requires two different administrators to approve the change.
This ensures that a single compromised laptop or stolen password is never enough to wipe the system.
Choosing the Right Defense
Not all storage is created equal. When evaluating a NAS system for ransomware protection, look for these specific capabilities:
- S3 Object Locking Support: This is the industry standard for immutability and ensures compatibility with major backup software like Veeam and Commvault.
- Compliance Mode: Ensure the hardware supports strict locking that cannot be overridden by the root account.
- Multi-Factor Authentication (MFA): This should be mandatory for accessing the management console.
- Secure Boot: This ensures the operating system itself hasn't been tampered with to bypass security controls.
Frequently Asked Questions
If a hacker has root access, can't they just factory reset the NAS?
Technically, yes. A hacker with physical access or IPMI (remote hardware management) access could factory reset the device. However, this formats the drives. While you lose the data, the hacker fails to decrypt or steal the data for extortion. The primary goal of immutability is to ensure data exists for recovery; a factory reset is a "scorched earth" tactic that is rare in ransomware attacks, as attackers usually want you to pay for a decryption key.
Does enabling immutability on an ISCSI NAS affect performance?
It depends on the implementation. Snapshot-based immutability on an iSCSI NAS generally has negligible performance impact because it only locks the pointers to the data blocks. However, if the iSCSI NAS system is calculating cryptographic hashes for every file to ensure integrity, there may be a slight overhead on write operations.”
Can I accidentally fill up my storage?
Yes. This is the biggest risk of Compliance Mode. If you set a retention policy of 10 years and fill the drive with backups, you cannot delete them to free up space. You must buy more storage. Proper capacity planning is essential when using strict immutability.
The Final Line of Defense
Cybersecurity is a game of layers. Firewalls, antivirus, and employee training are your first lines of defense, but they are permeable. Eventually, an attacker may get through.
When that happens, your NAS storage solutions must be the final, unbreakable wall. By implementing true immutability that treats internal administrators with the same "zero trust" skepticism as external threats, you ensure that your organization can recover from an attack without paying a ransom.




















Sign in to leave a comment.